By Don Okereke
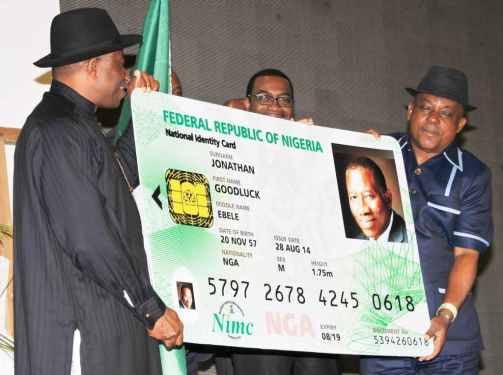
President Goodluck Jonathan recently launched a MasterCard-branded Nigerian National Electronic I.D Card amidst pomp and pageantry. The project is expected to gulp a whooping N30 billion! Tritely, there were cheers and allusions of how the e-I.D card project is one of the best things that has ever happened to Nigeria. Another transformation agenda, they tell us.
Hear Mr. Jonathan, “the card is not only a means of certifying your identity, but also a personal database repository and payment card, all in your pocket’’.
The National I.D Card Management Commission (NIMC) which happens to be the project leader is partnering with MasterCard which provides the payment technology; Unified Payment Services Limited functions as the payment processor and CryptoVision acts as the public key infrastructure and trust services provider.
Subtly suggesting a progression towards a ‘Big Brother State’, an ambitious NIMC says it is ‘’working with other government agencies to harmonize all identity databases including the Drivers, Voter registration, Health, Tax, SIM Card and that of the National Pension Commission into a single, ‘shared’ services platform’’. A ‘’Shared’’ services platform means these partners, most probably the Security agencies and other stakeholders will also have access to this humongous database.
This I.D Card claptrap is coming on the heels of a $40 million “Wise Intelligence Technology (WIT) System’’, an Open Source Intelligence Monitoring contract secretly awarded to Elbit Systems, an Israeli firm and also a bungled SIM Card registration exercise that gulped N6 billion. Proponents believe these moves are the panacea to the unprecedented criminality and the Boko Haram miasma stifling Nigeria. Notwithstanding, kidnapping, terrorism and insurgency continue to trend in Nigeria.
For the record, this writer advocates doing all that is rational and justifiable in our quest to protect Nigerians and Nigeria from internal, external aggression and wanton criminality. The notion and objective of the national electronic I.D Card looks good in theory but there are far-reaching, critical national security and fraud-related loopholes which this essay aims to highlight which must be appreciated, sorted if the purpose of the ID Card must be achieved.
There is a consensus in the global cyber security community that keeping personal information out of the reach of cyber criminals is increasingly becoming a mirage. Lilian Ablon, a security researcher with RAND Corporation contends that, ‘’the ability or plausibility of a cyber attack certainly outpaces the ability to defend.
Cyber criminals are extremely conversant with the jeopardy, loopholes inherent in the cyber world and are exploiting these weaknesses, employing a mishmash of technology (reverse engineering) and social engineering craftsmanship in order to short-circuit desired outcomes. In this age of BYOD (Bring Your Own Device), data breaches, proliferation of hacking, whistle blowing, cyber warfare/terrorism and espionage by State and non-state actor’s, the consequences of concentrating and sharing the private information (names, dates of birth, addresses, passport photos, fingerprints) of Nigerians with MasterCard et al and also outsourcing an internet surveillance contract to an Israeli firm no matter how well-intentioned will directly or indirectly have multiplier-effects. Edward Snowden and Bradley Manning are classic lessons that these days, insiders, not necessarily hackers are the biggest threat to data breaches.
Nigeria is currently struggling to rein in a rag-tag Boko Haram Sect whose masterminds and domicile are known. Contrast it with an unknown enemy, an insider (a cyber criminal or cyber terrorist) armed with just a laptop and internet connection, ensconced within our territory or in some remote part of the world. Cyber Terrorism/Warfare transcends physical boundaries and is increasingly tasking to forestall. With or without an electronic I.D Card, adherents of criminality and terrorism will still engage in their trade.
Masterminds of the September 11 terrorist bombing in the United States had official I.D cards, Passports or other identifying documents but they still managed to pull their stunt. I.D Cards no doubt aids investigations after an incident but it does not necessarily prevent the incident. No wonder ‘’the Australian Parliament shelved the prospect of issuing a national I.D Card after research showed that identification cards would not assist crime prevention because the police have more trouble finding evidence linking crimes with perpetrators than identifying criminals’’.
To help us appreciate the dire national security, fraud implications of a not-fool-proof e-I.D Card, let’s explore recent prominent data breaches and cyber attacks in the world. If the so-called advanced countries and world-class establishments are not immune to data breaches and cyber attacks, envisage the plausible scenario in Nigeria.
Lately, a Russian cyber crime syndicate was said to have amassed the largest known collection of internet data- encompassing 1.2 billion user names, password combinations and more than 500 million email addresses. Also recently, 75% of South Koreas population between the ages of 15 and 65 and more than half of the country’s total population may have had their personal information stolen by hackers. In 2010, a programme dubbed ‘’Stuxnet’’ recorded a phenomenal feat when it was used to attack, penetrate and disrupt Iranian nuclear power programme.
Not forgetting the streak of cyber attacks accredited to the Syrian Electronic Army. Bring to mind that a malware attack by cyber criminals on United States retail giant – Target led to the loss of 40 million credit, debit card and personal records of customers. It also emerged that another retail giant – Home Depot was attacked by cyber criminals with initial reports suggesting it may be higher than that of Target.
A group that goes by the moniker- Lizard Squad claimed it was responsible for a DDoS (Distributed Denial of Service) attack that took down Sony PlayStation’s network leading to loss of millions of data loss. In December 2006, 94 million Credit Card information of TJX Companies Inc was stolen by hackers. In 2005, hackers broke into CardSystems Database, one of the top payment processors for Visa, MasterCard, and American Express and stole 40 million credit card accounts.
The United States Secret Service say more than 1,000 U.S businesses may have been compromised by a Point of sale (POS) malware attacked dubbed ‘’Backoff’’. In Nigeria, we were told a while ago that the names, addresses, bank account details etc of some serving and retired personnel of Nigeria’s State Security Service was leaked online. Nairaland.com, Nigeria’s popular online forum suffered a malicious attack this year in which millions of users’ information was compromised.
Eugene Kaspersky, co-founder of Kaspersky Lab, an antivirus software firm asserts ‘’the amount stolen from banks, financial institutions, companies and individuals could be at least double the $100bn initially estimated three years ago’’. Analysts are of the opinion that many data breaches are but precursors to identity theft and identity cloning. A report from www.identitytheft.info suggests that approximately 15 million United States residents have their identities used fraudulently each year with financial loss totaling upwards of $50bn.
Let’s mull over the MasterCard financial transaction function of Nigeria’s electronic I.D Card. Having a MasterCard logo inscribed on Nigeria’s e-I.D Cards, a country of about 170 million people is surely a plus, a good marketing and publicity bargain on the side of MasterCard. However there is frenzy in Nigeria that ATM/electronic fraud is on the upward swing. Nigerian financial institutions are said to have lost about N2 billion to electronic fraud during the first and second quarter of 2014. Just few days ago, the EFCC declared one Godswill Oyegwa Uyoyou, an IT Staff of new generation bank, wanted in connection with a case of Criminal Conspiracy, Obtaining Money under False pretence and Electronic Transfer of Fund.
Mr. Godswill is alleged to have fraudulently connived with some scammers and hacked into his bank’s database and obtained the sum of Six Billion and Twenty-Eight Million Naira (N6.28b). Recall that most Automatic Teller Machines are powered by Microsoft’s Windows XP Operating System which is vulnerable to hacking more so since Microsoft has stopped issuing security patches, updates for bugs in Windows XP Operating Systems.
Discerning and concerned Nigerians are also worried with this arrangement which entails sharing biometric and sensitive personal information of Nigerians with a private foreign firm especially in this age of ‘Big Data’, and given the cache of top secret documents released by Edward Snowden revealing massive global metadata surveillance, eavesdropping, interception of radio, telecommunications, internet traffic monitoring and information sharing programs such as ‘’PRISM’’ with Microsoft as a partner, ‘’XKeyscore’’, ‘’Tempora’’, ‘’Muscular’’, ‘’Project 6’’, ‘’Ironavenger’’, ‘’Quantum Insert’’, by the intelligence agencies of the ‘’Five Eyes’’ namely -Australia (ASD), Britain (GCHQ), Canada CSEC), New Zealand, United States (NSA) and other mishmash of international collaborators such as – Denmark (PET), France (DGSE), Germany (BND), Italy (AISE), Norway (NIS), Switzerland (NDB), Spain (CNI), and Israel’s (ISNU).
The global super powers don’t even trust themselves as it emerged the mobile phone of German’s Chancellor Angela Merkel was allegedly tapped by United States intelligence agencies. Renowned technology firms headquartered in the West such as Microsoft, Apple, Verizon Wireless, the FaceBook, Yahoo!, Google etc of this world are said to be either covertly or overtly complicit. This explains why most countries are wary to award certain critical national security contracts to foreign firms. Aftermath of the allegations of spying leveled against the NSA, Germany swiftly expelled CIA’s station officer in Germany and subsequently cancelled its contract with Verizon Wireless, a US firm.
The Germans and some other countries are mulling the possibility of reverting to manual typewriters to counter hi-tech espionage. In June 2014, Chinese state-run TV dubbed Windows 8 a ‘security threat’ over allegations that Windows 8 Operating System is a tool for espionage. The Chinese contend that Windows 8 harvests private metadata and sends same back to Servers in the United States.
The Chinese government consequently banned the use of Windows 8 Operating System for Government Computers. In the same vein, use of Chinese-made Huawei products is banned by the US government over a similar allegation. Sequel to the NSA spying revelations, India considered a policy that would ‘’compel companies to maintain part of their IT infrastructure in-country, give local authorities access to the encrypted data on their Servers for criminal investigations, and prevent local data from being moved out of the country’’.
The giant of Africa is going on the reverse direction. No thanks to two daft swoops a.k.a. #TacticalManeuvers (apologies to the DHQ) vis-à-vis the internet surveillance contract and the latest e-I.D Card deal, Nigeria effectively outsourced its very critical national security databases (names, addresses, phone numbers, passport photos, fingerprints etc) to two robust partners – Israel and the United States on a platter of gold. One wonders if Nigeria’s national security think tank ever carried out a due diligence before these deals were consummated?
Life is quid pro quo! As they say, to him much is given, much is also expected of him. Nigerian citizens are coaxed into volunteering their priced personal information on the guise of an e-I.D Card believing their personal information are in safe hands thus it behooves establishments charged with handling these data to ensure their utmost safety. Hence the National Identity Management Commission (NIMC) must strictly adhere to Section 5 (g) of the Commission’s Act which mandates it to, ‘’ensure the preservation, protection, sanctity and security (including cyber security) of any information or data collected, obtained, maintained or stored in respect of the National identity Database. Folks responsible for data security must be well trained to be highly efficient. Financial institutions must invest in cutting-edge banking software that will forestall the aforesaid unintended consequences.
Granted Section 37 of the 1999 Constitution (as amended) barely stated that the ‘’privacy of citizens, their homes, correspondence, telephone and telegraphic communications is hereby guaranteed and protected’’, one is not aware that Nigeria has a well-defined Data Protection Law.
In line with international best practices, it is high time the National Assembly brainstormed, passed a comprehensive Data Protection Law which must inter alia, stipulate legal, regulatory framework, guidelines and safeguards for storing, using personal data and also stringent penalties for defaulters. If the #needful is not done, this may be a national disaster waiting to happen.
Please we implore the National Assembly to expedite passage of the National Cyber Security Bill into a law.
Finally, a poser: with an estimated 1,400 or more illegal entry points to Nigeria and with millions of illegal aliens resident in Nigeria, any assurance aliens will not obtain the e-ID Card?
It’s not uhuru yet!
Don Okereke is a security analyst/consultant, writer/blogger, change agent and ex-serviceman
www.donokereke.blogspot.com
Twitter: @donokereke
Telephone: +234 708 000 8285
Get more stuff like this
Subscribe to our mailing list and get interesting stuff and updates to your email inbox.